A team for more data security in the cloud

July 2020
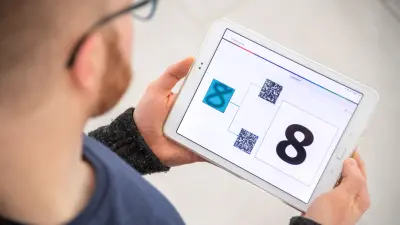
Putting together a picture from multiple different pieces is the principle behind solving a puzzle. Sven Trieflinger and his team at Bosch Research spend their working hours looking at puzzle pieces. The IT specialists at the research campus in Renningen are dedicated to protecting data in the cloud from unauthorized access. And that is where the puzzle principle comes into play.

Thanks to cryptographic protocols, the system is able to process data without having to put the pieces of the puzzle back together, despite the fragmentation. Trieflinger heads up a team of cloud and security experts that is in charge of implementing various different technologies designed to protect privacy within the scope of the SPECS Confidential Computing Platform. SPECS stands for security- and privacy-enhanced computing services.
Wide use of the data encryption software
The complex service, which has been undergoing development since 2017, is currently available as a prototype. In the months ahead, it will undergo testing based on specific use cases. Made up of three experts for cloud technologies in Renningen and five security experts in Pittsburgh, USA, the team is currently working with colleagues from the Bosch divisions on four specific use cases for this technology. “At the moment, we are focusing on internal use,” researcher Sebastian Becker says.
One promising use case comes from the Automotive Aftermarket division: “The operator of a Bosch service workshop manages his business using software from Bosch,” says Becker, describing the circumstances. “As a result, sensitive data is transmitted to the cloud.” Why is the data sensitive? “Because it might contain information about the workshop’s sales, for example,” he explains.
On account of the General Data Protection Regulation, or GDPR, processing workshop customers’ personal data also poses a problem, he says. Since May 2018, all EU member states have been subject to stricter data protection legislation. The GDPR significantly expands the obligation of companies to ensure the security of user data and to handle such information responsibly.
“SPECS makes sure that Bosch is unable to see this sensitive data while allowing the workshop operator to still offer services on this basis.” A corresponding prototype is slated for completion by the end of 2020 and will be tested in initial European markets next year.
In addition to this example, Bosch Research is developing further use cases for the SPECS technology.
Collaboration with start-ups on data security
This year, the SPECS team partnered with two start-ups that develop secure solutions for databases. Building on their technology, Trieflinger and his colleagues are working on a proof of concept outlining that the analysis of the workshop data is possible while upholding trade secrets and maintaining the privacy of workshop customers. “We are combining both technologies, allowing us to achieve a unique level of protection in data analysis,” Trieflinger explains.
Edgeless Systems
The start-up Edgeless Systems is developing a secure database to protect data while it is being stored and processed. A special mechanism involving modern processors makes sure that the data is not even accessible for system administrators.
Aircloak
The second start-up, Aircloak, is developing an anonymization filter that can be used with a database to prevent information that lets recipients draw conclusions as to data subjects (in this case: the workshop customers) from leaving the database.
“Without data encryption, it’s like living in a glass house – even if it’s not the neighbors who are snooping on you.”
Data security solutions gaining importance
Trieflinger is certain that solutions for more data security will continue to grow more important, not least because connectivity and the role played by data are constantly increasing. “Because trust is the foundation for successful business relationships, technologies that support the secure and responsible use of data are gaining importance.”



