Trustworthy computing – data sovereignty while connected

Jointly use data without sharing it – a vision born in the early 80s after Andrew C. Yao published his seminal work on Protocols for Secure Computations– is approaching reality thanks to major advances in cryptography. Our research on trustworthy computing aims to lift this technology into the cloud and provide Bosch customers with new levels of data security and privacy.
Loading the video requires your consent. If you agree by clicking on the Play icon, the video will load and data will be transmitted to Google as well as information will be accessed and stored by Google on your device. Google may be able to link these data or information with existing data.
More than 50% of consumers
have security and privacy concerns regarding the Internet of Things
Data sovereignty in a connected world
Bosch has committed itself to high ethical standards when handling its customers’ data. In our research on trustworthy computing, we strive to complement these ethical guidelines – called the Bosch IoT Principles – with technology built to live up to these standards. At the heart of this endeavor is the belief that people should be able to exert control over their data. Bosch Research is working on making this data sovereignty possible in the Security and Privacy Enhanced Computing Services (SPECS) division.
“Our solution makes it possible to keep data encrypted throughout while it is transmitted, saved and then stored – and even while you are working on it. To do this, we break the information down into individual parts and distribute it across various clouds. Cryptographic protocols make it possible to compute this distributed data. Only once the parts of the results of the computation are put back together does the whole picture make sense again.”
Sven Trieflinger, Head of SPECS at Bosch Research

Secure data – not just in the smart home
The smart home is one of the possible future areas of application in which trustworthy computing may be used. With the SPECS platform solution from Bosch Research, it will be possible in the future to process the data that the smart home collects about the user in encrypted form. The resident’s privacy can thus be protected without them having to forgo the benefits of digital smart home applications. The researchers are developing further use cases hand-in-hand with experts from various Bosch divisions:
Agriculture
With SPECS, farmers can get harvest forecasts without having to disclose trade secrets to the service providers.
Autonomous driving
A well-founded and up-to-date database is indispensable for the realization of highly automated driving applications. This requires test drives during the course of vehicle development. With SPECS, the personal data generated in this context in particular can be effectively protected throughout the processing chain.
Automotive workshops
The operators of service workshops can develop the business free of any concerns with the help of cloud-hosted software. Sensitive data which allows conclusions to be drawn regarding turnover, for example, is no longer visible to software and infrastructure providers.
Economy of Things
Distributed Ledger Technologies (DLT) can improve trust in digital offerings because the exchange of values between economic units is no longer done through centralized platforms, but rather through decentralized and distributed protocols. SPECS further ensures even greater confidentiality in this, as the exchange of information and the initiation of a value exchange can be implemented securely and without a centralized platform player.
Software-in-the-Loop systems and simulation-based system and software development
The development of complex systems which are used, for example, in the field of autonomous driving requires collaboration between companies and the use of simulation technologies for early and economical validation of the systems on the basis of common, cloud-based integration platforms. Here, SPECS can protect the parties’ intellectual property when introducing the models into a joint co-simulation for such systems.
Cryptography in an industrial context
These breakthroughs rely on end-to-end data protection that keeps data safe from unauthorized access throughout the whole data life cycle – in transit, at rest and in use. The underlying cryptographic techniques are called secure multiparty computation (MPC) and homomorphic encryption. Both have a long history in the academic world, but until recently their limited efficiency has largely prevented industrial application.
Today, performance is no longer the major inhibitor for real-world use. For that reason, our research at the intersection of cryptography and distributed systems now focuses on removing other barriers to industrial application. In this way we want to create truly practicable, scalable, and dependable solutions that are ready to prove their mettle in highly demanding application domains such as the automotive industry.
Bosch Research can rely on an established network of innovative partners when overcoming the associated challenges. For example, there is currently a collaboration with the start-ups Edgeless Systems and Aircloak within the context of the Open Bosch program. Within this collaboration, Bosch Research and the start-ups are working together on a system for analyzing workshop data while maintaining privacy and trade secrets.
The start-up Edgeless Systems is using Trusted Execution Environments as the basis for the development of a scalable solution for protecting data during processing. Here, a special feature of modern processors ensures that the data itself is not accessible to system administrators. The second start-up, Aircloak, is developing a filter which can be set up around a database and which ensures that no information that would allow conclusions to be drawn about the data subjects leaves the database. “We are combining both technologies and thus achieve a level of protection that is unique in data analysis,” explains Sven Trieflinger of Bosch Research.
In order to be able to closely follow future developments in the area of industrial application of secure multiparty computation and to influence upcoming standardization in accordance with our company values, Bosch joined the MPC Alliance in December 2020. The MPC Alliance is a group of nearly 40 companies with the shared mission to accelerate the adoption of MPC technology.

Summary
The Bosch IoT Principles enshrine our commitment to high ethical standards where our customers’ data is concerned. Data sovereignty is a key tool for fulfilling this obligation while offering cutting-edge, data-driven solutions that are competitive in a connected world.
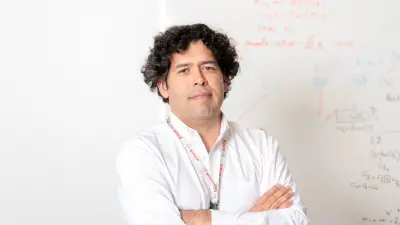
Get in touch with our expert
Dr. Sven Trieflinger